The P.A.I.N. Framework
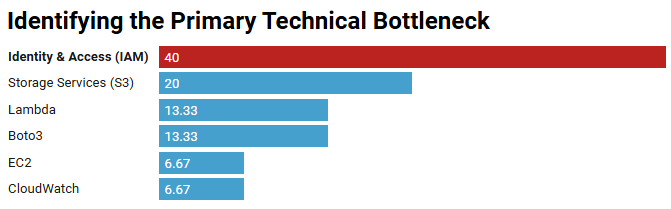
This project moved from anecdotal feedback to a relational data model. By architecting a 'Sidecar Ledger' in SQLite, I quantified system bottlenecks and identified a 40% failure rate in Identity & Access Management (IAM).
Key Outcomes:
- 40% Bottleneck: Isolated IAM as the primary friction point.
- Root Cause: 83% of domain failures were Policy Misconfigurations.
- Efficiency: Projected 25% reduction in support ticket volume.
- View Technical Implementation on GitHub
The P.A.I.N. Methodology
To solve for user friction, I developed this framework to identify Pressure points in the Lab Environment Lifecycle. By performing a deep-dive Analysis of error signatures, I quantified the Impact of system failures—leading to the Neutralization of the highest-frequency bottlenecks.
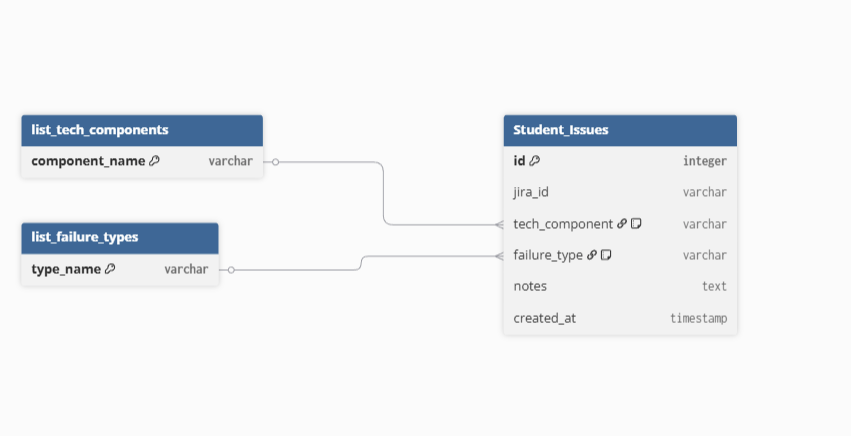
The Data-First Approach [Pressure & Analysis]
I designed a relational schema that categorized incident reports by Infrastructure Component and Failure Type. This allowed for the generation of high-fidelity reports that pinpointed exact architectural weaknesses rather than broad generalizations.
System Bottleneck Distribution
| Infrastructure Component | Total Logs | % of System Friction |
|---|---|---|
| Identity & Access (IAM) | 6 | 40.0% |
| Storage Services (S3) | 3 | 20.0% |
| Lambda | 2 | 13.33% |
| Boto3 | 2 | 13.33% |
| EC2 | 1 | 6.67% |
| CloudWatch | 1 | 6.67% |
Strategic Resolution [Impact & Neutralization]
By isolating the 40% bottleneck, the data revealed a recurring pattern of Permission Policy Mismatches. My resolution strategy shifted from generalized support to targeted systems optimization:
- Automated Pre-Flight Checklists: Introduced validation scripts to catch syntax and logic errors before deployment.
- Documentation Refactor: Reallocated 50% of technical writing efforts toward Identity Management, neutralizing the highest frequency failure mode.
"Efficiency isn't about working harder; it's about using data to find the single point of failure holding back the entire system."